By Sean Magann
With an expanding variety of uses, smartphones, laptops and tablets are among the most useful tools in business. These devices are providing convenience for companies and customers alike, such as mobile point-of-sale (POS) systems, while also providing sales and business executives more options to handle business tasks while away from their desks.
Different versions of laptops are even being made to accommodate different types of executives. The everyday traveler may choose a smaller and lighter laptop with less functionality whereas stationary employees might consider a bulkier option with increased storage and processing capabilities.
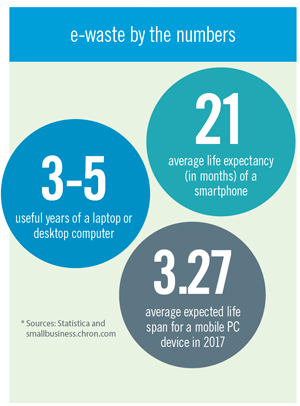
Regardless of the user or the usage, upgrades to faster devices with newer operating systems and more robust apps mean that technology cycles are growing shorter, and the resulting e-waste is challenging organizations of all sizes to deal with the proper disposition of these electronic assets. This is a growing responsibility for the Investment Recovery department. That’s where the process of IT asset disposition (ITAD) comes into play.
What is ITAD?
If you are not familiar with the term ITAD, you are not alone. The term references the rapidly growing field of information technology asset disposition. ITAD is the process of disposing of IT equipment in a safe and responsible manner. A solid ITAD strategy is a crucial component of any IT life-cycle management strategy.
The ITAD process can include:
- Redeployment—reuse of assets within an organization
- Remarketing—resale of assets to a third party in their entirety
- Recovery—reuse of assets for parts
- Recycling—reducing assets to commodity form
All technology devices will eventually have a need for this service. Businesses large and small as well as consumers are affected, and many of these devices store personal and confidential data. Devices may include:
- Laptops, tablets, cell phones and smartphones
- Servers, routers and other networking equipment
- Printers or multifunction devices, fax machines and more
The management of retired IT assets has for many years been focused on the reuse of commodities rather than on the reuse of parts or the equipment as a whole. However, more e-waste recycling companies and their customers are realizing the benefits of reusing equipment when and where possible. Not only does equipment reuse add value to the recycling process, it is also the most environmentally friendly choice.
Transitioning from a recycling company to an ITAD
company forces operational changes. Metrics such as weight may have been appropriate for recycling streams but ITAD companies also measure throughput units.
While identification of remarketing value is extremely important, this does not mean metal separation and commodities are not. Eventually all devices will reach the end of their useful life. The recycling of commodities will always be an important component in dealing with obsolete equipment and is something technology recyclers should (and will) continue to invest in, in conjunction with other ITAD operations.
With recycling representing just one part of ITAD, there are several other services available as well that are outlined as follows:
Maximizing Value
Services focused on capturing the value from these old devices are managed in two ways: redeployment or refurbishment. Redeployment is the process of returning assets to an organization for internal reuse. Redeployment encourages use across different departments and allows the company to avoid the purchase of new equipment. Otherwise, if an item isn’t needed internally, it can be refurbished and remarketed either a whole unit or as individual components, such as memory and hard drives. This allows the client to receive the maximum returns on their IT assets.
Destruction of Data
The destruction of stored data is often a customized service for the client. There are various methods for data erasure that can be performed, some allowing the hard drive to be reused and some rendering the device obsolete.
Overwriting or clearing data is a common solution for organizations who want to remarket their equipment. This process replaces written data with random data. Data can be cleared or “wiped” a single time or go through multiple passes. Generally, hard drives manufactured after 2007 require only a single-pass wipe. The cost and value of the drive are all considerations, but ultimately it’s the client’s decision.
Regardless, it is critical for this service to be performed by certified professionals to guarantee data erasure. Older methods for erasing data, such as trash can and delete, or shift and delete, do not remove data. Even the Gutmann wiping method, involving a series of 35 patterns that are run over the region, holds patterns that are now outdated. Methods that were developed for use on older devices and require many wiping procedures are proving irrelevant for today’s hard drives.
In addition to wiping considerations, the type of hard drive makes a difference on the desired method for data erasure. Solid- state drives store data in flash memory chips, which allow for no moving parts. They are smaller, more durable, use less energy and are cooler than traditional drives. However, solid-state drives are more expensive and cannot go through standardized wiping methods for confidential data destruction. These drives need custom wiping and have a limited number of write and erase sequences, but do hold a high resale value.
Purging and/or shredding of hard drives can also ensure data destruction. Purging represents the degaussing of media, which is a magnetic data erasure process. Since a degaussed hard drive cannot be reused, this is typically followed by the physical destruction of the hard drive for commodity value. Devices sent with a request to purge data typically store highly sensitive information (no desire for reuse), contain unusable hard drives or are drives that were made before 2007. Pre-2007 hard drives require a three-pass wiping process but the value of the drive doesn’t support the cost of multiple passes. Otherwise solid-state drives cannot be degaussed and are sent immediately for destruction. The shredding and/or physical destruction of the hard drive can occur whether or not the hard drive has been degaussed, so sometimes it can be easier to eliminate the step of degaussing and go straight to destruction.
Harvesting Software
A service offered by some ITAD vendors is to take an inventory of installed software prior to wiping or destruction of the hard drive. Removing, transferring or canceling licenses is a component that most software asset management (SAM) programs might include in their reporting but forget to take action on. Ensuring this software is followed up on can save companies a great deal of money when managing large quantities of devices.
Reporting
In dealing with evolving inventories and various types of equipment, detailed reporting can be critical to ensure accuracy. Every IT asset should have the type, make, model, serial number, installed software, condition, drive erasure verification and asset capture serialization report tracked and readily available to reference at any time. If the asset is being managed by a vendor, you should have some sort of access to an online portal where certificates of destruction and sustainability can also be retrieved as needed.
Policy Compliance
Two primary industry standards, e-Stewards and Responsible Recycling Practices (R2), help guide consumers and businesses during their ITAD vendor selection. In an industry sprinkled with bad players who might bandon warehouses of hazardous equipment or ship devices to areas without recycling processes in place, assistance in comparing vendors is critical. The two standards are similar in process and procedures and often compete with each other on a public stage. Regardless of the certifications, it is important that the firm generating the material audit the prospective ITAD vendor. Sims Recycling Solutions holds the R2 certification and encourages all customers to visit any of their global facilities.
Some additional global industry certifications include:
- Asset Disposal and Information Security Alliance (ADISA)
- HM Government
- Transported Asset Protection Association (TAPA)
- AS/NZS 4801 Occupational Health and Safety Management Systems
- EfbV Germany (German waste management regulation)
- Metaal Recycling Federatie (MRF) Netherlands
- Microsoft Authorized Refurbisher (MAR)
- WEEELABEX (WEEE label of excellence)
While all of these ITAD service options are important, data and physical security remain critical components of eliminating vulnerabilities. When changing the location and function of a device, security breaches become more likely to occur, making security part of the initial removal processes as well as throughout the device’s final disposition.
Data typically at risk can include:
- Proprietary data—e.g., new product info, product designs
- Customer/patient data—e.g., credit card info, Social Security numbers
- Regulatory compliance data—e.g., local and global requirements, industry regulations (HIPAA/GLBA, etc.)
Conclusion
The selection of a competent vendor to properly handle ITAD is a critical decision for an Investment Recovery department. The consequences of putting company data at risk can include upsetting customers and stockholders, damaging a company’s reputation, costing the company penalties from fines and sanctions, and potentially putting executives at risk of civil or criminal prosecution. While most companies already maintain an IT asset management program, integrating end-of-life IT assets into that program can prove beneficial to maximize device value and minimize risk.
This is a recap of a presentation delivered at the 2015 Investment Recovery conference in Chicago. Sims Recycling Solutions a leading provider of IT asset disposition services.
Sean Magann
Vice President, Sims Recycling Solutions
www.SimsRecycling.com